Enterprise networking in public cloud
Cloud networking has generally been a bit of a challenge - especially at scale, and especially in the enterprise. And for a very good reason. It was designed to be simple.
However the simplicity of the features, added complexity as engineers created work arounds. One key use case, transit routing, created a lot of these challenges. Transit routing, which is routing traffic via a network segment it is not destined for, to reach its destination was a feature larger organisations needed but was not available natively. Enter the transit VPC, where your favourite flavour of router or firewall, was spun up in a VPC that would provide transit between multiple VPC’s and often your private data centre.
The problem with transit VPCs is that they are somewhat unruly. You are typically implementing multiple expensive firewalls, adding a bunch of VPNs, monitors and scripts and then having to manually manage security policies (unless you further script that). It slows you down, costs you more and can be somewhat brittle.

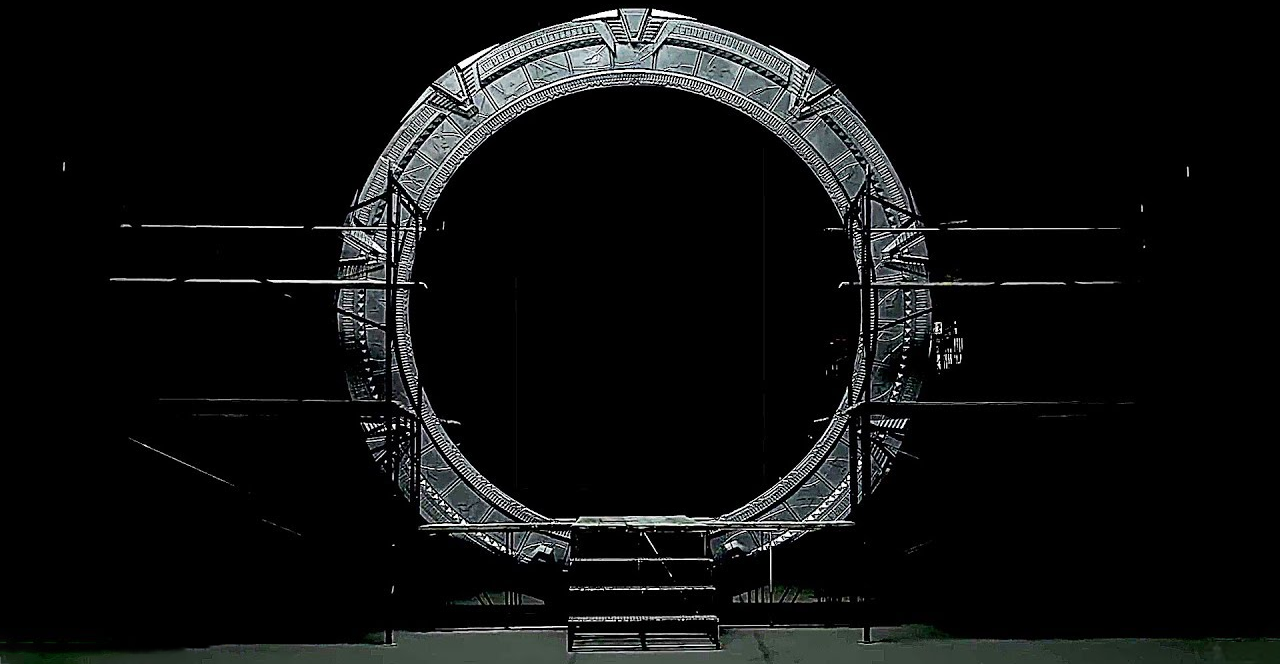
Introducing AWS Transit Gateway
So last year when AWS announced the Transit Gateway, it was very much welcomed… apart from one small detail that is. It did not support Direct Connect, another near necessity for enterprise customers. And so we waited...
But now the waiting is over. AWS have announced AWS Transit Gateway with support for Direct Connect. As with most services, this is being rolled out region by region, however it is likely to be generally available in your chosen location within the next couple of months.
A better way
What this allows us to do is implement AWS Transit Gateway in place of our own homebaked, third party firewall setup and and still be able to share an Internet Gateway, VPNs to our Data Centre and Direct Connect with multiple spoke VPCs.
You may wonder what this means for network security? In my opinion this only becomes better. Instead of using granular controls through cloud native features like security groups within your spoke VPC’s, but then coarse-grained controls on your traditional firewall in your transit VPC, you can now implement granular controls throughout your entire cloud setup, including the egress/ingress of your public cloud. While you could do this on your traditional firewall, implementation and management became a nightmare. While with software defined rules (which you can template or manipulate through APIs) it is both efficient and effective to now implement these.
Your traditional firewalls still provide a level of separation between your private traditional data centre and your reimagined, public cloud, software-defined data centre.

If that isn’t enough, you can also plug in one of my favourite tools for managing cloud security, Dome9 (now owned by Check Point). Dome9 will help visualise, manage and audit your cloud-native security ensuring a position of compliance and best practice. Again, because your security is now software-defined, it can do this in an extremely agile manner with dynamic monitoring and remediation of your security configuration.
If you need enterprise networking features for scalability, but still want the agility and flexibility of public cloud, check out AWS Transit Gateway. For the cherry on the top, also have a look at Dome9.